
The world of finance and the banking sector is simply blooming with the latest technological advancements. Their users are getting multiplied every single day. So, with an increased multiplicity of users for Mobile banking applications, the expectation with the applications is quite obvious. It should be robust, secure, and easy to use specifically if it is in finance-based apps.
Mobile banking is a quick and easy way to handle your finances, including checking your balance, financial transactions, paying bills electronically, and more. When your mobile application is facilitating so many activities, it is massively important for us to make mobile banking safe and scalable as per user needs.
Looking at the importance of mobile banking solutions, we decided to bring before you the factors that contribute to making mobile banking security a priority. The role of confidentiality security in mobile banking applications can never be underestimated. So, let’s take a look at some of the more popular mobile banking security issues. We will also discuss some points on how to deal with them using new technology and approaches.
1. Types of Mobile Banking Fraud Cases
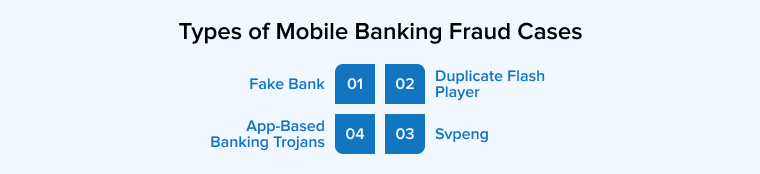
Here are the types of mobile banking fraud cases:
1.1 Fake Bank
In today’s time, mobile banking security researchers are continuously finding and preventing mobile app-based banking malware, trojans, phishing attacks, fake banking apps, and brute force attacks that are only fintech apps. And one of the biggest concerns is a fake bank. It is a spyware that monitors the payment verification messages or OTPs that are sent by the authorized banks to the clients. And when any mobile banking users get a verification code, the spyware copies the message and sends it to cybercriminals.
1.2 Duplicate Flash Player
Duplicate Flash Player is one type of video application that is a predatory eMail or an installed file via an infected SMS that comes with a malicious download link. This means that once the mobile device user installs this video app, it will ask for some permissions and then the malware of the application will start creating a dummy login screen that is visible to the user when he opens it the next time. So, if the user enters the credentials or bank login details once, the malware will copy all the data and send it to the database of the malicious users that the hackers can use later.
1.3 Svpeng
A senior malware analyst of Kaspersky lap, Roman Unuchek found a new adjustment of the mobile banking trojan Svpeng. It is a dangerous mobile banking-based malware. It is a trojan that can draw itself over other mobile applications and unofficial sources, can carry out financial transactions, offer itself permission to send and receive messages, read contacts, make calls, and access the device administrator rights.
1.4 App-Based Banking Trojans
Other mobile banking fraud cases include app-based banking trojans. These trojans are hidden in unrelated applications like tools or games that are downloaded by unsuspecting clients. These are the apps that are downloaded from unofficial sources. And they could contain malicious programs that lie dormant till the mobile user launches a banking app. Once any banking app is launched on the phone, the trojan springs to life and starts creating a pop-up overlay on the bank’s login page, and once the user enters their id and password, the trojan is passed on to the banking app login page.
2. Tips to Improve Mobile Banking App Security
Here are the tips to improve mobile banking app security are:
2.1 Advocate the Use of SIM Cards with NFC Technology
There is a lot of buzz around the security of mobile applications as there are many instances of confidential information leakage or financial loss and non-ethical hacking. There have been incidents when credit or debit card details are leaked or hacked. Many other malicious practices conceal the user data and use their financial records in the future.
When users are unable to go out in uncertain times, mobile banking is the safest option available. Not just this, there has been the incorrect practice of hacking the details from the cookies stored on mobiles or desktops. No security is assured. Therefore, customers are reluctant to perform web and mobile app support services through their mobile phones.
To save your enterprise from such unknown leakage of confidential information, we advocate the use of SIM cards for Credit and debit. Customers can easily download their credit card data onto their Near Field Communication SIM card using a SIM card embedded with NFC. This is another alternative to protect their account data in general, It enables you to carry a card and use it if your SIM card is nearby. It improves mobile banking security and eventually improves the performance and reliability of the app.
2.2 Add a Multi-Factor Authentication Feature to the App
The best part of financial business is that it has quickly taken up the pace and traversed from paper banking to paperless banking. In this process of transformation, there are many security checkpoints established by banks and banking software development companies. These points are called multi-factor authentication. By name, we have understood that there are multiple points assigned to check the authenticity of customers
Why do we need a multifactor authentication feature? Multi-factor authentication is like security checkpoints where if there is access to one password, the rest cannot be hacked. In other cases, one password is a link to several other passcodes and hence mobile banking systems have come up with several other options in defense. With this feature, there will be many security blocks the hacker has to go through like face recognition, fingerprint, and One-time password. This is an extra layer added to the safety of customers to protect them from breaches or hacks.
2.3 End-to-end Encryption to Save Information Leakage
When you perform digital transactions, there are two parties always involved – Of course one is the sender and another is the receiver. Like in an everyday instance, we see many people doing regular transactions through mobile apps or financial mobile payment gateways. Everyday users such as normal customers, retailers, cards, payment brands, and issuing banks play critical roles.
Every day, every year, billions of dollars worth of confidential data are shared. As a result, internet purchases have become a target for cybercriminals. To save consumers from this, businesses need to encrypt the transaction.
End-to-end encryption is a viable alternative to this enormous problem because it guarantees data security and stability. It is in charge of organizing safety checks and surveys. This is a safety measure for protecting businesses from fraud and unethical users.
2.4 Introduce Fingerprint Device In-App
For the safety of businesses, there have always been discoveries and innovations. Another vital innovation of the 21st century is the advent of fingerprint recognition. This is another safety layer for mobile apps. This saves the accounts from getting hacked by adding some layers. It is made taking into consideration multiple aspects such as browser, IP address, screen size, location, time, device type, location, and others. A fingerprint scanner is installed in the smart devices and it safeguards the information of users in the system itself. So if the device has your personal information and it gets into the hands of a hacker, then you don’t have to worry about it since it is sealed with your fingerprint details.
When your business develops a mobile banking application like this, you need to ensure that the details are sealed and there is no chance of data leakage. Your developers must know how to integrate this feature within the applications developed. Users from all domains- insurance, mortgage, eCommerce, retail, or any other industry can use this.
2.5 Real-Time Report Via Phone or Email Alerts
When you develop a banking app, there are various features apart from the safety ones that a business demands. The banking app offers businesses a fully-featured mobile application. This includes mobile banking facilities with loan options, mortgage services, personal loans, private loans, home loans, interest rates, online banking, credit card information, and similar other details. It also lets you know in case you have changed your savings account to current or salary-based accounts. All info is timely communicated in the best way possible.
With all this inevitable information stored in the application and each of these details is interlinked. Thus, when you develop the app link every single transaction with the history. This will also add the mobile number of the user. The addition of this functionality keeps the user informed about the transaction via emails or phone alerts. It could be an SMS or phone call.
2.6 Make Use of Behavior Analysis
The development of banking mobile applications has come a far way from where it started. It has now become the need of the hour. Businesses develop financial accounting software that is tailor-made as per the needs of the banks or financial sector. There are numerous details that are stored such as analyzing the time spent on the app, login locations, saved passwords, and other account activities.
This behavior analysis of the user is in favor and they raise a flag whenever there is any unusual activity taking place. Risks associated with the account are timely raised by the development resources online and necessary actions are also taken in real-time. This is an auto-generated feature that investigates all malicious practices and can inform the user of all types of suspicious concerns.
2.7 Data Breach
The security of applications is always questionable with hackers invading the private and confidential data of users. A data breach is one of the common challenges that businesses deal with in the existing system. If we go by the stats, Data breaches exposed 36 billion records in the first half of 2020.-RiskBased
When there is a data breach occurring for every business information, no data is safe. Hence we have to develop applications that safeguard our information is of great importance. Mobile banking applications store both types of data personal and business. They have ready access to users’ passwords, account numbers, and other credentials that hackers would like to have.
When placed on a mobile computer, such confidential information cannot be adequately secured. Mobile file systems are easy to crack. Installing security applications that secures your data from all types of breach. Furthermore, without a strong defense, an opponent only needs a range of advanced instruments.
The only way here is to stop relying on the standard way of development kits and find other secure data. Keep most of the information encrypted by using modern encryption algorithms that can be decrypted when the need arises.
2.8 PSD2’s Financial Consequences
The European Union has revised the Payment Services Directive (PSD2), which includes multi-factor authentication for online European payment. With this law, PSD2 requires financial institutions that maintain payment accounts to contest internet transfers made by users, such as card purchases, through two-factor authentication (2FA). This better authentication blends what the user recognizes, like a password or PIN, with something the user has, like a code created by a mobile app or a biometric identifier.
This online method of payment for international trading was brought to effect so that the transaction becomes more secured and protected between two bank accounts. This banking application will not allow any third-party company to get information about the customer without his/her consent. This is an added security to the mobile banking application to protect them from fraud.
3. Conclusion
We know that innovations in technology are occurring at an unprecedented speed. The use of smartphone mobile banking has made banking go digital. The advancements have also given rise to cyber crimes and thus users are reluctant in utilizing the technology. As a rescue, the banking sector is growing with innovation and has developed the discussed developments in the field of mobile banking application securities. Integrating the above-mentioned features with the help of app development companies will help customers curb the majority of all the security challenges to overcome fraud.






In the past few years, digital transformation is spanning rapidly across the banking landscape. But along with this security is the most important thing in the banking industry. I really liked that you have mentioned how to improve mobile banking app security with its problems and solutions. Thank you for sharing this informative article.